North Korean Hackers Use Fake Job Interviews to Spread Malware
North Korean hackers are once again targeting people in the cryptocurrency industry — this time using a new trick involving fake job interviews. A recent investigation by French cybersecurity firm Sekoia has uncovered a campaign they’ve named ClickFake Interview, where job seekers are lured into downloading a dangerous backdoor called GolangGhost.
You might be interested in: North Korean Hackers “the Lazarus Group” Attack Nuclear Engineers
A Fresh Twist on a Known Scam
This latest attack is believed to be a continuation of a broader campaign known by several names like Contagious Interview, DeceptiveDevelopment, and Famous Chollima. These operations are linked to the well-known Lazarus Group, a hacking crew connected to North Korea’s intelligence agency.
What makes this new wave different is its focus on fake job interviews for non-technical roles — such as asset management, business development, and crypto product roles — instead of targeting developers like in past scams.
How the Attack Works
The attackers pose as recruiters from big-name companies like Coinbase, Kraken, Tether, Robinhood, and more. They approach job seekers through platforms like LinkedIn or X (formerly Twitter), inviting them to take part in a video interview.
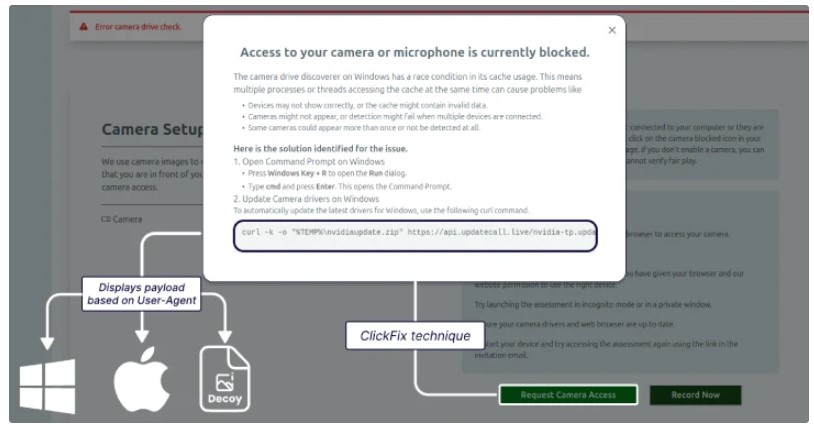
Victims are then directed to a fake video platform, usually branded as something like Willo, where they’re asked to record a self-introduction. Everything seems legit until they try to activate their webcam — that’s when a fake error message pops up.
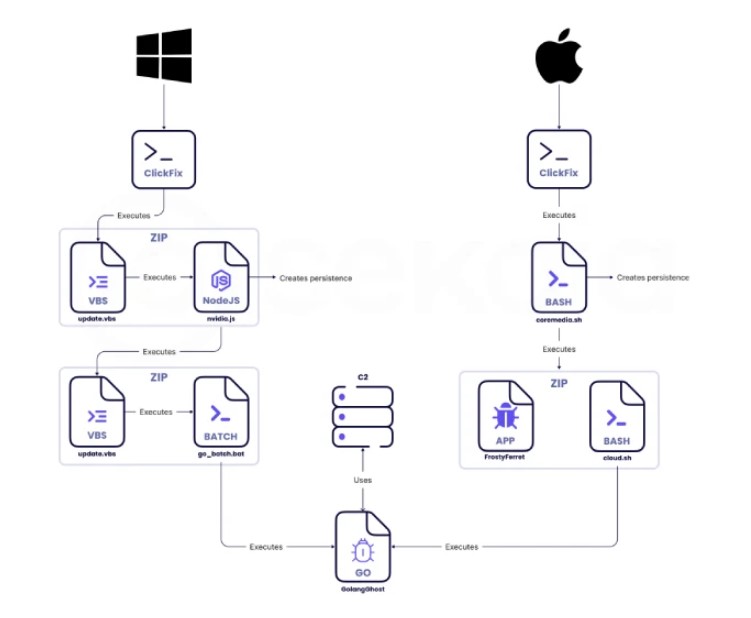
To fix the issue, the victim is told to run a command in the terminal or command prompt, depending on their operating system. This step secretly installs GolangGhost, along with another malware module called FROSTYFERRET.
Platform-Specific Tricks
-
Windows users are told to run a Visual Basic script via
curlthat eventually launches GolangGhost. -
macOS users are asked to run a shell script that triggers the same outcome.
The FROSTYFERRET tool then shows a fake Chrome window asking for camera access. Once the user enters their system password, the malware sends the information to a Dropbox folder, likely to help the hackers access services like iCloud Keychain.
What GolangGhost Can Do
Once installed, GolangGhost gives attackers remote access to the victim’s computer. It can:
-
Upload and download files
-
Steal browser data
-
Send back system details
This level of access means the hackers can swipe cryptocurrency, private info, or even control the device directly.
The Bigger Picture: North Korea’s Global Cyber Push
The campaign is just one part of a larger operation. North Korean tech workers are now pretending to be remote developers in Europe, not just the U.S. They’re using fake identities, sometimes claiming to be from countries like Vietnam, Japan, Italy, or Ukraine, to land freelance jobs on platforms like Upwork, Freelancer, and Telegram.
According to Google’s Threat Intelligence Group, there’s been a sharp increase in these fraudulent IT workers across Germany, Portugal, and the U.K. They’re taking jobs in:
-
Web development
-
Bot creation
-
CMS platforms
-
Blockchain projects
To avoid detection, these workers use crypto, TransferWise, and Payoneer to get paid. They’re even recycling or stealing GitHub portfolios to appear more legitimate.
From Freelancing to Extortion
Recently, these fake workers have also started extorting their employers. If fired or discovered, they threaten to leak company data unless they’re paid off.
They also target companies with Bring Your Own Device (BYOD) policies, since personal devices often lack the security features of corporate hardware.
Wake-Up Call for Europe
Cybersecurity experts are warning that Europe is not taking this threat seriously enough. While the U.S. has cracked down on these schemes, North Korea has simply shifted its focus to Europe where regulations and awareness are weaker.
“This isn’t just an American problem anymore,” said Jamie Collier from Google’s security team. “North Korea has a long history of adapting its cyber tactics to stay ahead.”