Outlaw Botnet: A Growing Crypto Threat
Cybersecurity experts have recently uncovered detailed information about a botnet known as Outlaw, also referred to as Dota. This Linux-based malware is designed to spread automatically by taking advantage of servers that use weak SSH passwords. By exploiting these vulnerabilities, the malware can quietly infiltrate systems and begin its harmful activities without raising immediate alarms. This type of attack poses serious risks not only to individual devices but also to larger organizations that rely on secure network infrastructures.
You might be interested in: New Phishing Service Exposed
Outlaw’s primary danger is that it turns infected systems into cryptocurrency miners. This process uses the machine’s resources to solve complex mathematical puzzles, allowing the attackers to earn digital coins. Over time, the continuous mining process can slow down the performance of a server, increase operational costs, and even lead to hardware damage due to sustained high usage. The attackers, believed to be from Romania, have been active since at least 2018, using simple shell scripts to execute their attacks and maintain control over compromised systems.
How It Works
Outlaw infiltrates systems by launching brute-force attacks on SSH (Secure Shell) servers. Essentially, the malware tries a long list of common username and password combinations until it finds one that works. Once access is granted, the malware installs its own SSH keys into the system. These keys give the attackers persistent access, ensuring they can return to the system even if the original vulnerability is later secured.
After establishing access, the malware immediately starts mining cryptocurrency. Cryptocurrency mining involves using a computer’s processing power to solve difficult mathematical problems, which in return generates digital coins. The mining process is not only resource-intensive but also cleverly hidden from casual observation. The use of simple shell scripts in the attack process makes the operation both efficient and challenging to trace back to its origins.
Infection and Spread
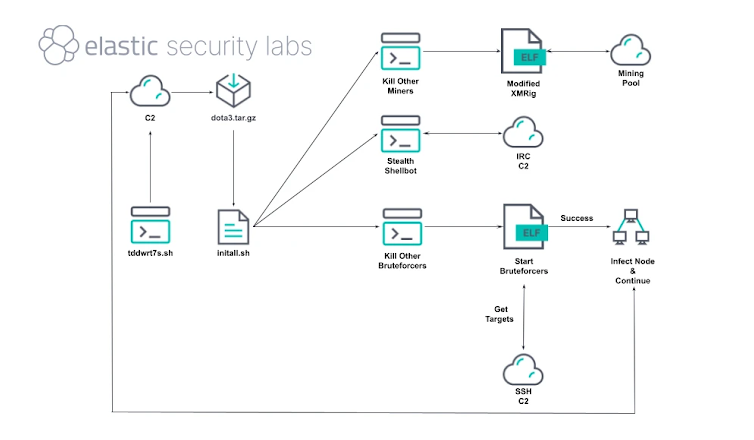
The infection process employed by Outlaw is systematic and multi-layered. The attackers first deploy a dropper script called “tddwrt7s.sh” that downloads an archive file named “dota3.tar.gz.” Once downloaded, the archive is unpacked to reveal the mining software along with other components needed to sustain the attack. During this stage, the malware also removes any traces of previous infections and actively terminates competing mining software to ensure maximum resource availability for its own operations.
A critical component of the malware is an initial access module known as BLITZ. This module not only helps infect the current system but also scans for other vulnerable SSH servers in the network. BLITZ retrieves a list of potential targets from a remote command server, allowing the malware to continuously propagate across systems. This coordinated approach enables the attackers to build a large, resilient botnet with relative ease, maintaining a robust foothold across many compromised devices.
Exploits and Remote Control
Outlaw’s attack strategy is not limited to brute-force methods. The malware also takes advantage of specific vulnerabilities in Linux and Unix systems. For example, it exploits known flaws such as the Dirty COW vulnerability (CVE-2016-5195) and another weakness identified in 2016 (CVE-2016-8655). Additionally, systems that rely on Telnet with weak passwords are particularly vulnerable to these types of attacks. By exploiting these issues, the attackers can gain elevated access and further secure their hold on the compromised system.
Once the malware is in control, it uses a tool called SHELLBOT to enable remote management. SHELLBOT allows the attackers to execute any shell command they desire on the infected system. This can include downloading additional harmful software, launching distributed denial-of-service (DDoS) attacks to overwhelm target websites, stealing login credentials, and exfiltrating sensitive information. The ability to control systems remotely in this manner makes Outlaw a versatile and evolving threat that can adapt quickly to countermeasures.
Mining Efficiency and Persistence
To optimize its cryptocurrency mining operations, Outlaw checks the CPU capabilities of the infected machine. It then enables hugepages on every core—a memory management feature that increases efficiency by allocating larger blocks of memory. This adjustment boosts the performance of the mining process, allowing the malware to extract more digital coins over time. In addition, the malware employs a tool called kswap01 to maintain a constant and reliable connection with the attackers’ command server.
Persistence is a key feature of Outlaw. The malware uses straightforward yet effective tactics, such as scheduling tasks with cron jobs, to ensure it restarts automatically even after a system reboot. This makes it difficult for system administrators to completely remove the infection. Moreover, by utilizing custom XMRig miners and communicating through IRC channels, the malware remains flexible and capable of receiving updates or additional commands from the attackers. Publicly available scripts further help it hide its tracks, complicating efforts to detect and mitigate its presence.